Throughout human history, there have been many threats to the security of nations. These threats have brought about large-scale losses of life, the destruction of property, widespread illness and injury, the displacement of large numbers of people, and devastating economic loss. Recent technological advances and ongoing international political unrest are components of the increased risk to national security.
Throughout human history, there have been many threats to the security of nations. These threats have brought about large-scale losses of life, the destruction of property, widespread illness and injury, the displacement of large numbers of people, and devastating economic loss. Recent technological advances and ongoing international political unrest are components of the increased risk to national security.
This particular type of training is geared to response personnel (HAZMAT, fire, police, EMT’s, hospitals etc.). Since September 11, 2001 (and prior to this date) staff members have been trained by EPA, Department of Justice, Connecticut State Fire Academy and FEMA. The programs (which can be found in our training section) range from Weapons of Mass Destruction – Domestic Preparedness to DOJ COBRA (Chemical, Ordnance, Biological, Radiological) training. In the aftermath of 9-11 it is important that services and industry are at least aware of and prepared for whatever the future brings.
Vulnerability Assessments
The first step in a risk management program is a threat assessment. Threat/vulnerability assessments and risk analysis can be applied to any industrial, educational, and healthcare facilities, as well as organizations.
What is a threat assessment?
Threat assessment is a structured group process used to evaluate the risk posed by a person, typically as a response to an actual or perceived threat or concerning behavior. All facilities face a certain level of risk associated with various threats. The threat assessment considers the full spectrum of threats (natural, criminal, terrorist, accidental, etc.) for any given facility/location. Whatever the threat facility owners have a responsibility to limit or manage risks from these threats.
Once the plausible threat(s) has been identified, a vulnerability assessment must be performed and a vulnerability assessment checklist built.
- Vulnerability: A flaw or weakness in system security procedures, design, implementation, or internal controls that may result in a security breach or a violation of the system’s security policy.
- Threat: The potential for a specific vulnerability to be exercised either intentionally or accidentally
- Control: measures taken to prevent, detect, minimize, or eliminate risk to protect the Integrity, Confidentiality, and Availability of information.
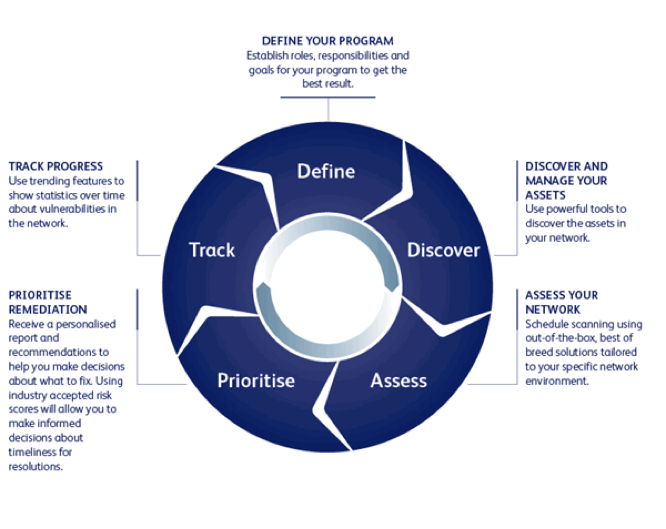
- Vulnerability Assessment: The process of identifying, evaluating, determine the level of protection and prioritizing (or ranking) the vulnerabilities in a system.